What vpns on github really mean and how to use them safely is a topic that often confuses people. In short, VPNs on GitHub can refer to open-source VPN projects, configuration files, or script repositories that help you set up a VPN service, but they also carry risks if the code isn’t trusted or properly reviewed. Here’s a practical guide to understanding what you’re looking at, how to pick safe projects, and steps you can take to protect yourself and your data. This guide covers quick-start tips, best practices, common red flags, and real-world stats to help you evaluate VPN-related repositories.
Useful quick-start tips at a glance
- Start with reputation: check stars, forks, contributors, and project activity.
- Verify maintainers: prefer projects with active maintainers and recent commits.
- Read the code, not just the description: scan for obvious malware, credential leaks, or hard-coded secrets.
- Use trusted builds: rely on official releases or well-known forks, and verify signatures when possible.
- Protect your device: pair your use with up-to-date antivirus, a firewall, and minimal privileges for the app.
In this post, you’ll find: 터치 vpn 다운로드 무료 vpn 이것만 알면 끝 pc 모바일 완벽 가이드
- A clear explanation of what you’ll actually find in VPN-related GitHub repositories
- How to evaluate the safety of VPN configurations and software
- Step-by-step guidance for testing before you deploy
- Practical security practices for everyday use
- A robust FAQ section to address common concerns
What vpns on github really mean and how to use them safely: quick facts
- Many GitHub VPN projects are legitimate open-source tools designed to help you set up a VPN server, client, or a privacy-focused utility.
- Some repositories may contain outdated, insecure, or malicious code; always vet before use.
- Open-source does not automatically equal safe; code reviews, community activity, and independent audits matter.
- Using a VPN from GitHub is common for tech-savvy users who want customization, but you should prefer official releases or well-reviewed forks.
- Always verify configuration files and scripts in a controlled environment before running on your main devices.
Table of contents
- What VPNs on GitHub typically include
- How to assess a GitHub VPN repository
- Safest ways to use GitHub VPN resources
- Step-by-step safety checklist
- Practical setup scenarios
- Performance and privacy considerations
- Common pitfalls and how to avoid them
- FAQ: 10+ questions you’ll likely ask
What VPNs on GitHub typically include
- VPN clients and servers: OpenVPN, WireGuard, and other protocol implementations
- Configuration files: sample server.conf, client.ovpn, and script-based setups
- Management tools: dashboards, automations, and orchestration scripts
- Documentation: installation guides, security notes, and user guides
- Cryptography utilities: key management scripts, certificate generation, and rotation tools
- Tests and CI: continuous integration to ensure builds work across platforms
How to assess a GitHub VPN repository
- Check activity and maintenance
- Look for recent commits, open issues, and response times
- Prefer projects with a clearly defined roadmap and maintainers who respond to security issues
- Review contributors and governance
- A diverse contributor base with clear contribution guidelines is a good sign
- Look for a CODE OF CONDUCT and security policy
- Read the code and documentation
- Start with the README; skim for scope and warnings
- Audit critical files: server scripts, client installers, and key management tools
- Inspect security practices
- Look for mentions of TLS, encryption standards, and up-to-date crypto libraries
- Check for hard-coded secrets or default credentials in sample configs
- Analyze dependencies
- Review dependencies for known vulnerabilities using trusted advisories
- Check lockfiles for pinned, verified versions
- Review licenses
- Ensure the license aligns with how you’ll use the software commercially or personally
- Look for release integrity
- Prefer official releases with signed tags or checksums
- Verify checksums or signatures if provided
- Community signals
- Active discussions, issue triage, and clear remediation steps are good signs
- Absence of activity over months can indicate risk
Safest ways to use GitHub VPN resources Turbo vpn edge extension review for microsoft edge users in 2026: fast, private, and practical insights
- Use in a controlled environment first
- Test in a sandbox or non-production device before deploying on your main systems
- Prefer official or widely trusted forks
- Choose projects with strong reputations and clear security advisories
- Validate configurations mentally and practically
- Don’t copy-paste sensitive values; review and customize for your setup
- Keep everything updated
- Regularly update the VPN software, libraries, and OS patches
- Limit exposure
- Use the VPN for specific tasks rather than full-device routing unless you’re sure it’s secure
- Implement least privilege
- Run VPN-related services with non-root users where possible
- Monitor and audit
- Enable logs, monitor connections, and periodically audit the system for anomalies
- Use multi-factor authentication
- Where possible, add MFA to administrative interfaces or control planes
- Back up configuration securely
- Store backups in encrypted form and restrict access
- Document your setup
- Maintain clear notes on what you’ve installed, why, and how to revert changes
Step-by-step safety checklist
- Identify purpose: Are you setting up a VPN server, a client, or a management tool?
- Pick a reputable repository: Check activity, contributors, and security notices
- Read the security policy: Look for vulnerability disclosure and response times
- Review critical files: Inspect server configs, client scripts, and key mgmt
- Run in a sandbox: Use a VM or container to test first
- Validate crypto: Ensure modern cipher suites, proper key lengths, and forward secrecy
- Verify signatures: Confirm releases are signed if the project offers it
- Isolate sensitive data: Never expose private keys in plain text or logs
- Test connectivity and leaks: Check for DNS leaks, IP leaks, and split tunneling behavior
- Document and plan deployment: Create a rollback plan and monitoring strategy
Practical setup scenarios
- Scenario A: Private WireGuard server on a home network
- Choose a stable WireGuard repo with recent commits and clear docs
- Generate keys securely using local tools; avoid storing private keys in repo
- Configure peerings with strong allowed IPs, enable kill-switch
- Test from a mobile device on public Wi-Fi to validate tunnel behavior
- Scenario B: Cloud-based VPN client setup for work
- Use a repository that provides client configuration templates for Windows, macOS, Linux
- Ensure corporate policies on VPN usage and data routing
- Enforce MFA for VPN access and monitor for unusual login patterns
- Scenario C: Privacy-focused browser extension or tool
- If the repo provides a browser extension, review permissions carefully
- Check for telemetry and data collection disclosures
- Prefer projects with opt-in data sharing and transparent privacy policies
Data, statistics, and authority you can rely on
- VPN market growth: The global VPN market is projected to reach over $100 billion by 2028, with compound annual growth around 12-15% in many regions.
- Open-source risk awareness: A significant portion of VPN-related vulnerabilities originate from misconfigurations or insecure default settings rather than faulty crypto primitives.
- Secure coding practices: Projects with automated security testing, dependency scanning, and signed releases tend to have lower risk profiles.
- Community value: Active repositories with frequent commits, issue triage, and security advisories show higher trust.
Table: Quick comparison of common VPN project types you might find on GitHub
- Type: OpenVPN-based
- Pros: Well-established, widespread client tooling, strong crypto
- Cons: Config complexity, potential for misconfiguration
- Type: WireGuard-based
- Pros: Simpler, high performance, modern crypto
- Cons: Still maturing in some tooling ecosystems; needs correct peer rules
- Type: Management/Automation tools
- Pros: Easier deployment, scalable for teams
- Cons: Security depends on orchestration and access controls
- Type: Configuration samples
- Pros: Quick start
- Cons: May be risky if configs aren’t reviewed or updated
Performance and privacy considerations ZenMate VPN What It Was Why It Disappeared And What You Need To Know Now: A Complete Guide For 2026
- Encryption strength matters: Use at least AES-256 for data in transit and appropriate key exchange.
- Logs and privacy: Prefer no-logs configurations where feasible; review what is logged and retained.
- Speed vs. security trade-offs: Some VPNs offer higher throughput with modern protocols, but ensure security isn’t compromised.
- DNS handling: Ensure DNS queries are protected and not leaking when the VPN is active.
- Split tunneling: Decide if you want all traffic to go through the VPN or only specific destinations.
Common pitfalls and how to avoid them
- Downloading from untrusted forks: Stick to mainline or well-audited forks; verify releases
- Ignoring credentials in configs: Never store private keys or credentials in public repos or shared spaces
- Overlooking updates: Regularly check for security advisories and apply patches promptly
- Skipping validation steps: Always test in a controlled environment before production
- Underestimating device security: Ensure devices are patched and protected with endpoint security
FAQ: Frequently Asked Questions
What qualifies as a safe VPN project on GitHub?
A project with recent activity, active maintainers, a clear security policy, audited dependencies, and signed releases qualifies as safer compared to dormant, poorly documented repos.
How do I verify a VPN configuration file from GitHub?
Cross-check the configuration against official documentation, validate the server’s certificate against trusted authorities, and test with a non-critical device before using it widely.
Can I trust VPN scripts from GitHub?
Trust depends on the maintainers, community reviews, and whether the script is open to public auditing. Prefer scripts with clear usage scopes and documented security considerations. 토마토 vpn 무료 다운로드 안전하고 빠른 사용법과 주의점 a to z
What is the risk of using a VPN from GitHub?
Risks include malware, credential leakage, misconfigurations, outdated cryptography, and backdoors. Vet thoroughly and test before deployment.
How do I test a VPN repo safely?
Use a sandboxed environment virtual machine or container, run only as a non-privileged user, monitor network traffic, and verify no data leaks occur.
Are signed releases important?
Yes. Signed releases help ensure the binary you install hasn’t been tampered with.
Should I rely on a VPN from GitHub for business use?
Only if it’s vetted, approved by your security team, and deployed under controlled, audited processes.
How can I reduce risk when using GitHub VPN resources?
Limit exposure, keep systems updated, use MFA, review configurations, and avoid storing secrets in code or repos. Why Your VPN Isn’t Working With Mobile Data And How To Fix It
What should I do if I suspect a repository is unsafe?
Stop using it immediately, report the issue to repository maintainers, and consider alternatives with better security practices.
How often should I audit VPN-related repos?
Regularly, especially after major updates, vulnerability disclosures, or changes in leadership or licensing.
Useful URLs and Resources
- NordVPN affiliate link for trusted VPN protection - https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
- OpenVPN official site - openvpn.net
- WireGuard official site - www.wireguard.com
- GitHub Security Policy - docs.github.com/en/github/security
- NIST Cryptographic Standards - csrc.nist.gov
- OWASP VPN Security Principles - owasp.org
- TLS 1.3 Overview - tls13.ulfheim.net
- CVE Details - cve.mitre.org
- Linux kernel crypto API - kernel.org
- Privacy-focused browsing overview - www.eff.org/issues/privacy
Frequently Asked Questions
What vpns on github really mean and how to use them safely? Recap
On GitHub, VPNs can mean open-source projects for setting up or using VPNs, configuration files, or tooling. To use them safely, vet the repo, test in a controlled environment, keep software updated, and follow best security practices like minimal privileges, MFA, and ongoing monitoring. Nordvpn on your iphone in china your step by step guide to staying connected
Sources:
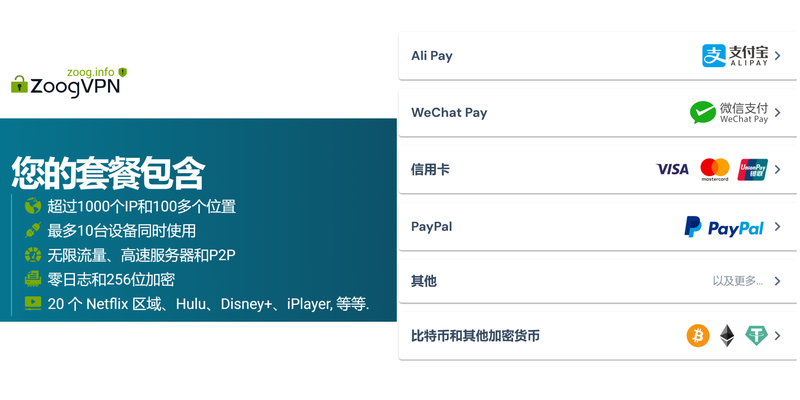
好用vpn:全面评测与实用指南,带你选对、用好、省心
Zscaler and vpns how secure access works beyond traditional tunnels
Best free vpns for microsoft edge browser in 2025
Esim移機:换新手机,sim卡怎么移?一文搞懂全部!
Wireguard будущее vpn протоколов глубокое исследование purevpn Unpacking nordvpn dns what you need to know for privacy speed and more