Finding secure vpns on github your guide to open source privacy
Finding secure vpns on github your guide to open source privacy is all about understanding how to vet open source VPN projects, what to look for in code, and how to protect your privacy when you use or contribute to VPNs hosted on GitHub. Here’s a practical, reader-friendly guide packed with real-world tips, examples, and checklists you can follow today. This post uses a step-by-step format and handy lists to make the material easy to digest, whether you’re new to open source or you’ve been around the block.
Quick facts to set the stage Softether vpn download 최신 버전 설치부터 활용까지 완벽 가이드
- Open source VPNs can be powerful for privacy, but not all forks and repositories are trustworthy.
- Look for active maintainers, transparent auditing, and reproducible builds.
- Always verify the software’s provenance before trusting it with sensitive data.
Useful resources you might want to save text only Apple Website - apple.com Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence GitHub Security Best Practices - github.com/github/security OpenVPN Community - openvpn.net WireGuard - www.wireguard.com Mozilla VPN - vpn.mozilla.org
Introduction: what you’ll learn and why it matters Finding secure vpns on github your guide to open source privacy is not just about grabbing a codebase and hoping for the best. It’s about building a mental checklist for privacy, security, and trust. In this guide you’ll find:
- A practical checklist to assess VPN projects on GitHub
- How to spot red flags like outdated dependencies, lack of audits, and fake forks
- A straightforward workflow to verify builds and configs
- A comparison of popular open source VPN projects and what makes them trustworthy
- Step-by-step tips for contributing safely and responsibly
What is an open source VPN and why GitHub matters
- Open source VPNs are powered by code that anyone can inspect. That transparency helps identify security flaws, supply chain issues, and privacy leaks.
- GitHub is a central hub for collaboration. When you’re evaluating a project there, you’re not just checking the code; you’re also assessing the team, governance, and response to security incidents.
Key terms you’ll see in this guide
- Open source: software with permissive licenses that allow anyone to use, modify, and share the code.
- Audit: a formal review of code and configurations by independent parties.
- Supply chain security: ensuring every piece of software you install comes from trusted sources and hasn’t been tampered with.
- Reproducible builds: the ability to recreate the exact build from source code, ensuring integrity.
- Maintainer: the person or team responsible for the project’s direction and security posture.
Step-by-step: how to find secure VPN projects on GitHub Surfshark vpn not working fix no internet connection fast 2026 guide
- Start with curate a short list of reputable projects
- Look for widely recognized names for example, projects with active communities, frequent commits, and documented security practices.
- Check the project’s README for a clear privacy policy, data collection statements, and scope.
- Examine the governance and activity
- Check the “Contributors” and “Maintainers” sections. A healthy project has multiple maintainers and regular commits.
- Review the issue tracker: are security issues acknowledged, triaged quickly, and fixed with documented releases?
- Review the code quality and security posture
- Look for unit tests, integration tests, and coverage reports.
- Check for explicit security advisories and a public vulnerability disclosure policy.
- Verify dependencies and supply chain integrity
- Inspect dependency files e.g., package.json, go.mod, requirements.txt for outdated or unmaintained libraries.
- Confirm the presence of reproducible builds and artifacts with checksums or signatures.
- Audit and testing visibility
- Search for third-party security audits or formal verification reports.
- Look for documented penetration tests or fuzzing results.
- Review privacy practices and data handling
- Understand what data the VPN collects, logs it might generate, and how long it’s kept.
- Check for privacy-preserving defaults and minimal data collection.
- Assess licensing and redistribution rights
- Ensure a clear license and compatible terms for your use case, especially if you plan to modify or distribute.
- Try a safe, staged deployment
- Use a non-production environment to test configuration defaults, DNS handling, and leak protection DNS leaks, WebRTC leaks, IP leaks.
- Validate routing behavior, kill-switch features, and split tunneling options.
- Verify builds and installation yourself
- Follow the project’s documented build steps exactly.
- Generate and verify checksums of binaries or containers.
- Contribute responsibly
- If you find a bug or improvement, follow the project’s contribution guidelines.
- Consider submitting security patches through proper channels rather than posting raw fixes publicly.
Hands-on checklist you can reuse
- The repository has an active maintainer and clear contribution guidelines
- There are recent commits and an active issue tracker
- A documented security policy or vulnerability disclosure process
- Dependencies are up-to-date with minimal known vulnerabilities
- There are reproducible build instructions and artifact verification
- A privacy policy or data handling statement is present
- The license is clearly stated and compatible with your use
- There is evidence of external security audits or third-party reviews
- The project has a tested kill-switch and leak protection mechanism
- You’ve tested in a safe environment before any real use
Portfolio-style comparison: common open source VPN projects Project A: WireGuard-based implementation
- Pros: Strong cryptography, small surface area, straightforward codebase
- Cons: Community is still maturing, some platforms require manual tweaks
- Security notes: Regular reviews, credible audits reported in public advisories
Project B: OpenVPN-based client and server
- Pros: Long-standing history, robust configuration options
- Cons: Larger codebase can introduce complex bugs, slower release cycle
- Security notes: Extensive documentation and widely used in enterprise environments
Project C: A newer, multi-hop VPN client
- Pros: Innovative routing options, active community
- Cons: Newer project, fewer independent audits
- Security notes: Watch for governance updates and audit reports
Different deployment models and what they mean for privacy Forticlient vpn not working on mac heres how to fix it
- Client-only VPNs: Focus on protecting the device’s traffic. Privacy depends on client integrity and logging policies.
- Server-based VPNs: Emphasize server-side protections. Ensure server operators follow strict logging and data retention policies.
- Mesh or multi-hop VPNs: Can improve privacy by not putting all traffic through a single exit point, but require careful configuration to avoid leaks.
Security and privacy best practices when using GitHub VPN projects
- Always validate signatures and checksums for builds you install.
- Prefer projects with explicit, audited security policies and transparent disclosure processes.
- Enable two-factor authentication on your GitHub account and use restricted deploy keys where applicable.
- Keep an independent monitoring plan: check release notes for security fixes and apply patches promptly.
- For sensitive use cases, run your VPN in a controlled environment and use tight firewall and DNS protections.
Common mistakes to avoid
- Rushing to install a VPN without verifying its provenance
- Relying on a single source for critical privacy tooling
- Ignoring updates or security advisories
- Underestimating the importance of proper configuration kill switch, DNS leak protection
How to contribute safely to open source VPN projects
- Start with small fixes or documentation improvements to understand the codebase.
- Join the project’s security channel or mailing list if available.
- If you find a vulnerability, follow the disclosure policy and avoid posting exploit details publicly.
- Share your environment setup and testing results to help others reproduce and validate fixes.
Real-world examples and case studies
- Case study: A well-known VPN project with few maintainers but frequent security updates demonstrates how transparency and rapid response can boost trust.
- Case study: A newer project that ran a successful bug bounty program, combined with public audits, shows how to build credibility from the ground up.
How to stay up-to-date with the latest open source VPN privacy news Is Mullvad VPN Good for China a Deep Dive into Bypassing the Great Firewall
- Subscribe to security advisories from recognized platforms
- Follow maintainers and security researchers on social channels
- Keep a personal watchlist of repositories with high privacy impact and regular activity
- Periodically review your own configurations and exposure
Maintenance and privacy hygiene for long-term use
- Regularly pull updates from upstream and test in a sandbox before rolling out
- Maintain minimal exposure: only enable necessary features and disable verbose logging in production
- Review data retention policies after major updates and during audits
- Document your own deployment decisions for future reference
Bonus: quick-start guide for beginners
- Step 1: Pick a reputable open source VPN project with recent activity and clear privacy policy
- Step 2: Clone the repository and read the security and contribution guidelines
- Step 3: Set up a test environment and build according to the docs
- Step 4: Verify the build with checksums and signatures
- Step 5: Configure the client with minimal logging and test for leaks
- Step 6: Monitor for updates and apply patches when disclosed
FAQ: Frequently Asked Questions
Is it safe to use open source VPNs from GitHub?
Open source VPNs can be safe if you verify provenance, check for audits, and follow best practices. Always review the code, governance, and security disclosures before using in production.
How do I verify a GitHub VPN project's integrity?
Check for reproducible builds, signed releases, and a documented process for vulnerability disclosure. Inspect dependency trees for outdated or vulnerable libraries. Softether vpn 최고의 무료 오픈소스 vpn 완벽 가이드 2026년 최신 정보 및 실전 사용 팁
What is a kill switch in VPNs?
A kill switch is a feature that blocks all network traffic if the VPN connection drops, preventing accidental data leaks.
Do open source VPNs log user activity?
It varies by project. Look for explicit privacy policy statements and data handling disclosures. Favor projects that minimize data collection.
How often should I update VPN software?
Regularly update to include security patches. For critical fixes, apply patches as soon as they’re released and verified.
Can I use multiple VPNs for extra privacy?
Multi-hop or chain VPN setups can improve privacy, but they require careful configuration to avoid leaks and performance issues.
What is supply chain security in VPNs?
It’s about ensuring every piece of software you install is sourced from trusted origins, with verified builds and signed artifacts to prevent tampering. Whats a VPN on TikTok and Do You Actually Need One? A Complete Guide for 2026
How important are external security audits?
Audits add credibility and oversight. They’re often the best indicator of a project’s commitment to security.
How do I contribute a security fix safely?
Follow the project’s disclosure policy, document your steps, and submit patches through the proper channels, avoiding public exposure of vulnerabilities.
What should I do after deploying a VPN from GitHub?
Test for leaks, verify privacy claims, monitor for updates, and keep an eye on advisories and community discussions for new risks or improvements.
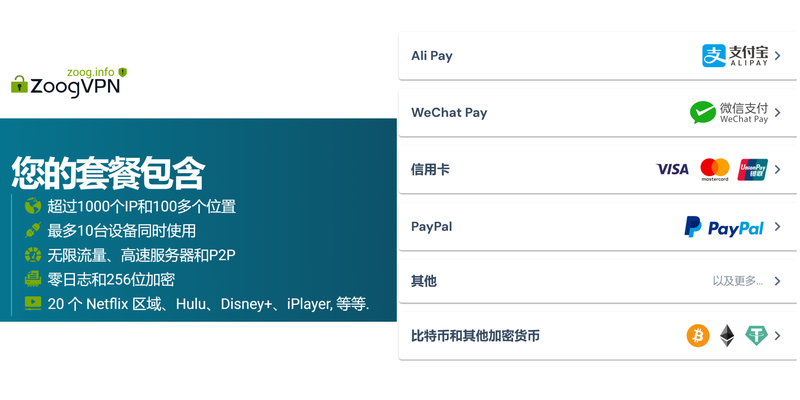
Affiliate note If you’re looking to add an extra layer of protection while exploring and evaluating VPNs on GitHub, consider a trusted option that’s easy to enable and monitor. NordVPN’s official page has been recommended by many privacy-conscious users for its comprehensive security features and straightforward setup. If you’re curious about adding a secure, well-supported option while you learn, you can check out NordVPN here: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
Tap into the right approach, stay curious, and keep your privacy needs at the center of every GitHub exploration. This guide aims to keep you grounded, informed, and ready to make smart choices without the fluff. Surfshark vpn very slow heres how to fix it fast: quick, practical fixes and setup tips for blazing-fast performance
Sources:
Microsoft edge 浏览器内置 vpn ⭐ 功能怎么用?全面指南与使用:现状、替代方案与安全要点
Nordvpn china does it work: how NordVPN, obfuscated servers, and stealth modes help bypass the Great Firewall in 2025
Windows vpn パスワード 表示方法:保存された接続情報を安全に確認する
Xbox edge vpn
Top des meilleurs vpn gratuits pour votre boitier android tv en 2025 Le vpn piu veloci del 2026 le abbiamo davvero provate