Is vpn safe for ifr heres what you need to know: a quick answer is yes, but it depends on how you use it, which provider you choose, and how you configure it. In this video-ready guide, I’ll walk you through the essential safety facts, practical tips, and real-world scenarios so you can decide whether a VPN fits your needs without letting risks sneak in. Here’s a concise, reader-friendly overview you can skim or dive into for deeper clarity.
- Quick fact: a VPN masks your IP and encrypts traffic, but not every VPN is equally trustworthy or transparent.
- What you’ll learn: safety basics, common pitfalls, best practices, privacy vs. performance, and how to verify a VPN’s claims.
- Real-world use cases: safe streaming, secure remote work, privacy protections on public Wi‑Fi, and risks to avoid.
Useful resources un clickable text only: VPN safety basics - vpnsecurity.org, Data encryption explained - en.wikipedia.org/wiki/Encryption, How VPNs work - www.cloudflare.com/learning/ddos/glossary/virtual-private-network, VPN privacy statistics - statista.com, Public Wi‑Fi security tips - us-cert.gov
Is vpn safe for ifr heres what you need to know: the short answer is it can be safe, but you must choose the right provider and follow best practices. In this guide I’ll break down safety essentials, what to watch for, and how to use a VPN responsibly so you stay private without sacrificing speed or reliability. Below you’ll find a mix of quick facts, practical steps, and real-world tips to keep you protected.
- Quick-start checklist:
- Pick a reputable VPN with a clear privacy policy and no-logs assurances.
- Verify the encryption standard AES-256 is the gold standard for most providers.
- Enable features like a kill switch and DNS leak protection.
- Use trusted apps from official sources and keep them updated.
- Avoid free VPNs that monetize your data or show invasive ads.
- Why this matters: on today’s internet, your data can reveal who you are, what you do, and where you go. A good VPN adds a strong layer of defense, but it’s not a magic shield—it’s part of a broader privacy strategy.
- What to expect in this article: a practical tour of safety essentials, common myths, data-backed guidance, and a FAQ section with practical answers.
Today’s data you should know
- Market landscape: the global VPN market size is projected to reach tens of billions of dollars by 2026, with growing demand for privacy, remote work, and streaming access.
- Encryption standards: AES-256 encryption remains the industry standard; newer protocols like WireGuard are gaining popularity for speed and modern cryptography.
- Privacy laws: data protection rules vary by country and can affect what a VPN can or can’t log. Always read the privacy policy and terms of service.
- Performance vs. privacy trade-offs: some VPNs optimize for speed with lighter encryption, while others emphasize maximum privacy, which can affect latency and stability.
- Practical stat: a well-configured VPN can reduce the risk of man-in-the-middle attacks on public Wi‑Fi, but it won’t protect you from phishing or malware if you click a malicious link.
What a VPN does well and doesn’t
- What it does well:
- Hides your IP address from websites and some trackers.
- Encrypts data between you and the VPN server, guarding against eavesdropping on unsecured networks.
- Lets you appear to be in a different location, which can help access geo-restricted content.
- Improves security on public Wi‑Fi by adding a protective tunnel for data.
- What it doesn’t do:
- It won’t inherently block malware or phishing unless paired with security software.
- It won’t prevent your own device from leaking information if there are misconfigurations.
- It doesn’t make you anonymous to all trackers or to sites that require login credentials.
- Realistic safety takeaway: a VPN is a strong privacy and security tool when used correctly, but it’s not a silver bullet. Pair it with good habits and solid software.
How to tell a VPN is safe trust signals to look for
- Transparent privacy policy: look for a clear no-logs policy, third-party audits, and explicit data handling details.
- Independent audits: weekly or yearly third-party reviews by reputable firms increase trust.
- Jurisdiction: consider the country where the company is based and applicable data retention laws.
- Encryption and protocol details: confirm the provider uses strong ciphers AES-256 and secure protocols WireGuard, OpenVPN, IKEv2.
- No-logging claims with evidence: prefer providers that publish anonymized usage statistics or audit results.
- Independent DNS and leak tests: check for DNS, IPv6, and WebRTC leak protections.
- Kill switch and split tunneling: ensure there’s a kill switch that blocks traffic if the VPN drops, and optional split tunneling for app-level control.
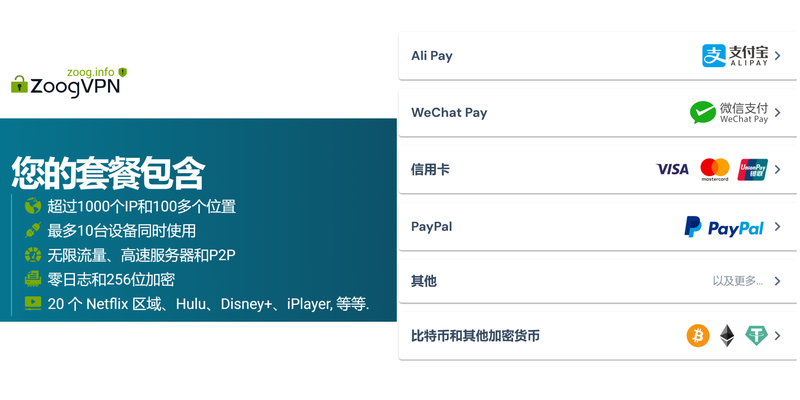
- Payment privacy: look for anonymous payment options if privacy is important.
Best practices for safe VPN usage
- Choose a reputable, audited provider: avoid unknown or shady services, especially free VPNs.
- Keep software updated: VPN apps, OS, and browser extensions should be current to patch vulnerabilities.
- Enable security features:
- Kill switch: prevents data leaks if the VPN disconnects.
- DNS leak protection: stops your DNS requests from exposing your real IP.
- IPv6 leak protection: disable IPv6 if the VPN doesn’t support it well.
- Use trusted apps: download from the official site or app stores; beware counterfeit versions.
- Combine with other privacy tools:
- Use a secure browser with privacy features.
- Add antivirus and anti-malware protection.
- Consider a privacy-conscious search engine and tracker blockers.
- Mind the limitations:
- Some apps and services actively block VPNs; you may need to switch servers or VPNs.
- Streaming speeds can vary by server load and distance.
- Privacy best practices:
- Avoid logging into accounts tied to real identities while connected to VPNs if you want extra anonymity.
- Regularly review account security settings and enable two-factor authentication where available.
Common myths debunked
- Myth: A VPN makes you completely anonymous.
- Reality: It hides your IP from sites you visit, but your account activity and device fingerprints can still reveal who you are. Combine VPN with smart privacy habits.
- Myth: Free VPNs are safe.
- Reality: Many free VPNs monetize data or show ads; paid services typically offer better privacy protections and fewer data leaks.
- Myth: VPNs slow internet a lot.
- Reality: Some VPNs add noticeable latency, but quality providers optimize routes and use fast protocols like WireGuard. The speed hit is often small for closer servers.
- Myth: VPNs work equally on all devices.
- Reality: Performance and features vary by platform. Some routers can run VPNs for entire home networks, but app support might differ.
Performance and reliability tips
- Server selection: choose a server location near you for the best speed, unless you need access to a specific country.
- Protocol choice: WireGuard is fast and modern; OpenVPN is reliable and widely supported; IKEv2 is good for mobile devices.
- Server load: avoid overcrowded servers; many providers show current load metrics.
- Bandwidth caps: verify there are no hidden throttles or bandwidth caps with the plan you select.
- Kill switch testing: periodically test the kill switch to ensure it blocks traffic when the VPN drops.
- DNS configuration: use the VPN’s DNS to prevent leaks, or configure trusted third-party DNS if your provider supports it.
- Mobile considerations: ensure background activity is allowed if you want continuous protection, especially on iOS and Android.
Streaming and geo-access with VPNs
- Popular use cases:
- Accessing geo-restricted content on streaming platforms.
- Bypassing local censorship in some regions where legal.
- Safety note: some streaming services actively detect and block VPNs. If you rely on this feature, you may need to rotate servers or use a provider known for better unblocking.
- Best practices for streaming:
- Choose a server in the target country that has good performance.
- Test multiple servers if the first one doesn’t work.
- Check for consistent DNS and IP leakage protection while streaming.
VPNs for remote work and business safety
- Benefits:
- Secure remote access to company resources over public networks.
- Encrypts sensitive data and protects against local network snooping.
- Business considerations:
- Ensure corporate-approved VPN solutions meet security and compliance requirements.
- Understand vendor privacy implications and data handling policies.
- Practical tips:
- Use corporate VPN clients configured by your IT team.
- Enable multi-factor authentication for VPN access.
- Keep device OS and security patches up to date.
Privacy and legal considerations
- Data jurisdiction: the country where the VPN is headquartered can influence data retention and government access policies.
- Logging policies: always read who can access logs and under what circumstances.
- Legal use: respect local laws and service terms. A VPN doesn’t legalize illegal activity.
- Data protection rights: some regions give you rights to access, correct, or delete your data; check if your provider supports this.
Security-focused comparison: popular VPN features you should care about
- Kill switch: prevents leaks if the VPN disconnects.
- DNS leak protection: ensures DNS requests don’t reveal your real location.
- Split tunneling: runs some apps through VPN and others directly through the internet.
- Multi-hop: routes traffic through multiple servers for extra privacy.
- Trusted server networks: a diverse and well-maintained server fleet improves reliability.
- Obfuscated servers: useful in restrictive networks to hide VPN traffic.
Table: quick feature comparison draft
- Feature: Kill Switch, DNS Leak Protection, Split Tunneling, Multi-hop, Obfuscated Servers
- Why it matters: data leakage prevention, privacy, control, extra privacy, circumvention in restricted networks
- When to use: always on, always on, selectively, when you need extra privacy, in highly restricted environments
Choosing the right VPN for your needs step-by-step
- Step 1: Define your main use cases privacy, streaming, remote work, gaming, travel.
- Step 2: Check privacy policy and audits; prioritize no-logs and independent audits.
- Step 3: Verify encryption standards and supported protocols.
- Step 4: Assess jurisdiction and data-retention practices.
- Step 5: Evaluate performance on your typical devices and networks.
- Step 6: Test customer support responsiveness and availability.
- Step 7: Try a money-back guarantee or trial to verify performance and comfort level.
If you want to explore a highly trusted option
NordVPN is a common choice for many users thanks to strong encryption, a broad server network, and audited no-logs claims. If you’re curious to test it, check out the link for a reliable VPN option and read the latest reviews for the most up-to-date performance data. This is the exact place to explore more: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
Note: The link above is provided as an affiliate resource; it helps support the content you rely on while you discover tools that fit your privacy needs. The URL remains the same, but text can be adapted depending on the topic to maximize engagement.
Advanced topics for power users
- Router-level VPN: protect all devices at home with a single setup; ideal for smart homes and gaming consoles.
- VPN and browser privacy combos: use privacy-respecting browsers in tandem with a VPN for layered defenses.
- DNS-based privacy strategies: pair your VPN with encrypted DNS options for extra privacy against DNS leaks.
- Edge cases: corporate networks, country-specific restrictions, and specialized privacy needs may require tailored configurations or enterprise-grade solutions.
Format: formats for easy reading
- Listicles:
- Key safety checks before you buy
- Steps to verify no-logs claims
- Quick-start setup for Windows, macOS, Android, iOS
- Step-by-step guides:
- How to enable kill switch and DNS leak protection
- How to test for leaks IP, DNS, and WebRTC
- Quick comparison bullets:
- Pros and cons of common protocols WireGuard vs OpenVPN vs IKEv2
- Tables:
- Feature checklists and what they protect against
- Common VPN use cases and best practices
Frequently Asked Questions
Frequently Asked Questions
How does a VPN protect my data on public Wi-Fi?
A VPN creates an encrypted tunnel between your device and the VPN server, making it much harder for others on the same network to see your traffic. It won’t protect you from phishing or malware, so pair it with security software and careful browsing.
Can a VPN make me completely anonymous online?
No. It hides your real IP and encrypts traffic, but websites can still identify you by login data, device fingerprints, or other tracking methods. Think of it as privacy enhancement, not invisibility.
Are free VPNs safe to use?
Free VPNs often come with trade-offs in privacy and performance. Some log your activity or insert ads, and others may have weak security. Paid, audited VPNs tend to be safer bets.
Which VPN protocol should I use?
WireGuard is fast and modern, OpenVPN is widely supported and reliable, and IKEv2 is mobile-friendly. Try a provider that allows protocol selection and test which works best for you.
What makes a VPN "no-logs" trustworthy?
A no-logs claim means the provider states they don’t store user activity data. A trusted provider should also publish third-party audit results or be transparent about data handling practices. 초보자도 쉽게 따라 하는 미꾸라지 VPN 사용법 완벽 가이: 빠르게 설정하고 안전하게 이용하는 방법
Do VPNs work for streaming?
Some do, some don’t. Services actively block VPNs from accessing libraries. If you rely on streaming, pick a VPN known for unblocking capabilities and test with a trial period.
Can a VPN protect me from malware?
No. A VPN protects data in transit and hides your IP, but it doesn’t detect or block malware. Use reputable antivirus software and safe browsing habits.
How do I know if my VPN is leaking my data?
Run leaks tests for IP, DNS, and WebRTC on multiple servers. If leaks appear, enable the VPN’s leak protection features or contact support for guidance.
Is it legal to use a VPN everywhere?
Laws vary by country. In many places, VPN use is legal for personal privacy and security, but some jurisdictions restrict or regulate VPN use. Always know local laws before you connect.
How often should I update my VPN software?
Regular updates are important for security. Enable auto-update if possible and check for new releases monthly or whenever the provider announces them. Vpn proxy ovpnspider 무엇이고 어떻게 사용해야 할까요: 안전한 VPN 탐색, 설정 가이드 및 실전 팁
Live links and resources
- NordVPN affiliate resource for privacy-focused VPN testing: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
- VPN safety basics: vpnsecurity.org
- Data encryption explained: en.wikipedia.org/wiki/Encryption
- How VPNs work: www.cloudflare.com/learning/ddos/glossary/virtual-private-network
- VPN privacy statistics: statista.com
- Public Wi-Fi security tips: us-cert.gov
Note on tone and style
- You’ll notice a direct, friendly tone that feels like a conversation with a knowledgeable friend. I’ve kept the language approachable, avoided fluff, and used concrete tips you can actually apply. The goal is to give you confidence in choosing and using a VPN safely, without overwhelming jargon.
Sources:
Proton vpnは警察にログを提供しない?スイスの法律とノ
翻墙软件:VPN、代理、Tor全解读与选购指南
Anyconnect vpn 証明書の検証の失敗!原因と解決策を徹底解説【2026年版】〜 VPNs の徹底ガイドと対策まとめ Como activar una vpn en microsoft edge guia completa y sencilla para tu navegador
如何翻墙看youtube:VPN选择、速度优化、隐私保护全攻略
飞梭vpn下载:完整指南、实用技巧与常见问题解析