Vpns proxies and zscaler whats the difference and do you need them? Quick answer: they’re different tools that serve related but distinct purposes. VPNs encrypt and route your entire internet connection through a remote server to protect privacy and access geo-restricted content. Proxies are intermediaries that forward your web requests, often for specific apps or browsers, sometimes without encryption. Zscaler is a cloud-based security platform aimed at enterprise users, combining secure web gateways, zero trust network access, and threat prevention. You might need one, two, or none depending on your goals—privacy, access, or enterprise security. Here’s a practical guide to help you decide.
- Quick fact: If you’re focused on personal privacy and browsing security, a reputable VPN is usually enough. If you want to protect a whole organization’s web traffic and enforce corporate security policies, a Zscaler-like solution is more appropriate.
- For individuals: VPNs offer broad protection and simpler setup. Proxies can be handy for geolocation testing or bypassing simple blocks but lack strong encryption. Zscaler is typically for businesses, not individuals.
- For teams: A VPN plus cloud security like Zscaler can deliver both secure access and policy enforcement across a distributed workforce.
Useful URLs and Resources text only, not clickable:
- NordVPN official site - nordvpn.com
- Zscaler official site - zscaler.com
- Wikipedia VPN - en.wikipedia.org/wiki/Virtual_private_network
- Proxy servers explained - en.wikipedia.org/wiki/Proxy_server
- Zero Trust Networking - en.wikipedia.org/wiki/Zero_trust_security
- Cloud security gateway overview - cisco.com
- Best VPN reviews 2026 - example.com
- VPN vs Proxy comparison - en.wikipedia.org/wiki/Proxy_server#Types_of_proxies
Quick guide: Vpns proxies and zscaler whats the difference and do you need them. If you’re new to the topic, think of it like this: VPNs protect your entire online journey; proxies protect specific browser requests or apps; Zscaler protects a company’s entire traffic with strict security policies. This post breaks down everything in plain English, with real-world examples, checklists, and a couple of quick setup steps you can try today.
- What you’ll learn:
- The core differences between VPNs, proxies, and Zscaler.
- Scenarios where each makes sense.
- How to choose the right tool for personal privacy vs. business security.
- Common myths and mistakes to avoid.
- Format you'll find useful:
- Side-by-side comparisons
- Quick-start setup steps
- Pros and cons lists
- Real-world use cases
- A mini FAQ at the end
What is a VPN, and how does it differ from a proxy?
- VPN stands for Virtual Private Network. It encrypts all traffic from your device and tunnels it through a remote server.
- Proxies act as intermediaries for specific requests, often without encryption or broad coverage.
- Zscaler is a cloud-based security platform for enterprises that combines secure web gateway, zero trust access, and threat protection.
Key differences at a glance:
- Scope: VPN covers the entire device; proxies typically cover individual apps or browser traffic; Zscaler covers all web traffic for a business with policy enforcement.
- Encryption: VPNs usually encrypt traffic; proxies may not; Zscaler encrypts and inspects traffic as part of security policy.
- Management: VPNs are typically user-side or IT-managed for individuals; proxies require config per app; Zscaler is centralized as a security service.
- Use cases: Privacy and bypassing geo-restrictions VPN; app-level anonymity or testing proxy; corporate security, access control, and threat prevention Zscaler.
How VPNs work simple view
- You install a VPN app.
- Your device routes traffic through a VPN server.
- Data is encrypted between you and the server, masking your IP and location.
How proxies work simple view
- You configure a browser or app to use a proxy server.
- Requests go to the proxy, which forwards them to the target site.
- Depending on the proxy type, your traffic may not be encrypted.
How Zscaler works enterprise focus
- It sits in front of users’ internet traffic.
- It uses secure web gateways, cloud firewall features, and zero-trust access to verify users and devices.
- It inspects traffic for malware, policy violations, and data leaks, regardless of user location.
VPNs vs proxies: typical use cases
VPN use cases
- Personal privacy and anonymity online.
- Bypassing geo-restrictions for streaming or travel.
- Securing public Wi-Fi connections cafes, airports.
- Avoiding ISP bandwidth throttling in some situations.
Proxy use cases
- Quick access to region-locked content in a browser.
- Lightweight testing of how a site looks from different geolocations.
- Masking your IP for a single app or browser session without affecting other apps.
When a proxy can be enough and when it isn’t
- Pro: Lightweight, simple to set up for specific tasks.
- Con: No full-device encryption; potential leaks if misconfigured; lower reliability for privacy.
When VPNs are a better fit
- You want comprehensive protection across all apps and services.
- You need steady, civilization-grade encryption AES-256 is standard.
- You’re concerned about public Wi-Fi risk and privacy.
Zscaler: is it right for you or your organization?
- Zscaler is designed for organizations with remote workers, multiple offices, or a distributed workforce.
- Features include secure web gateway SWG, zero trust network access ZTNA, cloud firewall, data loss prevention DLP, and threat intelligence.
- Pros:
- Centralized policy enforcement.
- Strong security posture and visibility.
- Scales with large teams and complex networks.
- Cons:
- Overkill for individuals or small teams.
- Requires IT involvement or managed service integration.
- Potential user friction during policy changes or login.
Enterprise-friendly alternatives for individuals include consumer VPNs with robust privacy policies, plus optional local proxy testing environments if needed.
How to decide what you need
If you’re an individual focused on privacy and general security
- Start with a reputable VPN.
- Look for:
- No-logs policy with independent audits.
- Strong encryption AES-256.
- Good speed and reliable servers in locations you care about.
- Transparent privacy policy and data handling.
- Optional: Use a proxy only for occasional, non-sensitive tasks like quick location testing.
If you’re a small business or large organization
- Assess workload, remote access needs, and security requirements.
- Consider a VPN for remote access to internal resources and a SWG/ZTNA approach for web traffic.
- Evaluate Zscaler or similar platforms for centralized policy enforcement, threat protection, and compliance.
A practical checklist
- Do you need to protect all device traffic or just specific apps?
- Do you require encryption for all traffic, including on public networks?
- Are you subject to data protection laws or industry compliance requirements?
- Do you have IT resources to manage security software, or do you prefer managed services?
- What’s your budget and desired user experience?
Real-world scenarios and examples
Scenario 1: A remote worker who travels a lot
- Best fit: VPN for device-wide protection plus a basic security posture.
- Why: Easy to set up, consistent protection on laptops and phones, good for public Wi-Fi.
Scenario 2: A teen gamer who wants lower latency and location testing
- Best fit: Proxies for testing different regions in games, plus a VPN if privacy on public networks is a concern.
- Why: Proxies can help with region testing; VPNs can add privacy but may affect latency.
Scenario 3: A mid-sized company with multiple offices
- Best fit: Zscaler-like SWG and ZTNA solution for centralized security plus a VPN for remote access to internal resources.
- Why: Central policy control, threat protection, and scalable access for distributed teams.
Security considerations and myths
- Myth: VPNs are enough for privacy. Reality: VPNs protect data in transit, but they don’t guarantee anonymity. Your VPN provider can see traffic metadata unless they have strict no-logs practices.
- Myth: Proxies keep you safe online. Reality: Proxies may not encrypt traffic or protect against malware; they can also leak IPs if not configured correctly.
- Myth: Zscaler replaces the need for VPNs. Reality: Zero trust networks and SWGs complement VPNs; depending on your setup, you may use both for layered security.
Important security tips:
- Choose VPNs with audited no-logs policies and independent testing.
- Prefer VPNs with Kill Switch features to prevent IP leaks if the connection drops.
- Use multi-factor authentication MFA for any enterprise security portal.
- Keep software updated to reduce vulnerability exposure.
- For businesses, implement data loss prevention DLP and threat protection policies.
Performance and usability considerations
- VPNs can impact speed due to encryption overhead and distant servers. Choose a VPN with a broad server network and optimized routes.
- Proxies can be faster for simple tasks but may expose you to leaks or misconfigurations.
- Zscaler-related deployments can introduce authentication steps, but modern implementations try to minimize user friction with seamless SSO and agent-based enrollment.
How to set up a basic VPN on your device step-by-step
- Choose a reputable VPN provider with strong encryption and a good privacy policy.
- Install the VPN app on your device Windows, macOS, iOS, Android.
- Sign in with your account and select a server location.
- Enable features like Kill Switch and Auto-Connect if available.
- Connect and test your IP address to confirm the change.
- Test a few websites to ensure there are no unexpected blocks or DNS leaks.
Notes:
- If you’re using multiple devices, install the app on each one or enable device-wide protection where available.
- For streaming, pick a server close to your location for better speeds, or one that specifically supports streaming.
How to test your VPN, proxy, or Zscaler setup
- Check for IP address changes via a site like whatismyip.com.
- Run a DNS leak test to ensure your DNS requests aren’t leaking to your ISP.
- Validate latency with a quick speed test to ensure you’re getting acceptable performance.
- For proxies, test with the specific app you configured to verify traffic is routing through the proxy correctly.
Pros and cons: quick reference
- VPN
- Pros: Strong overall encryption, broad protection, easy to use.
- Cons: May reduce speed, provider trust is critical, may require subscription.
- Proxy
- Pros: Quick setup for specific tasks, can be free or low-cost.
- Cons: Usually not encrypted, limited protection, can leak IPs.
- Zscaler enterprise
- Pros: Centralized security, strong threat protection, policy enforcement.
- Cons: Not for individuals, IT involvement needed, potential user friction.
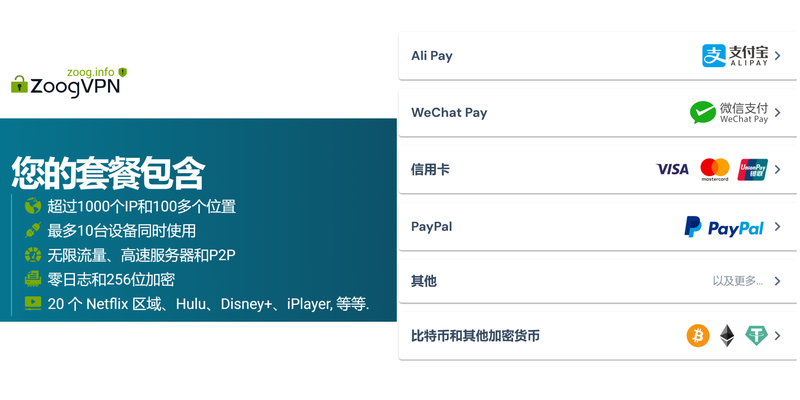
Comparing pricing and availability
- Consumer VPNs typically range from $2 to $15 per month depending on features and length of commitment.
- Proxies can be free or cost a few dollars per month for premium proxy services; performance and reliability vary.
- Zscaler pricing is enterprise-level and typically negotiated per user with tiered features like SWG, ZTNA, and DLP.
Common questions people ask
- Are VPNs illegal? Most VPN use is legal in many countries, but some regions restrict or ban VPNs for certain activities.
- Do proxies reveal my real IP? Depending on the proxy type and configuration, leaks can occur if not set up properly.
- Can I use VPN and proxy together? Yes, but you’d usually choose one for a given task. Combining them can complicate troubleshooting.
- Is Zscaler only for big companies? It’s designed for enterprise use, but some managed service providers offer Zscaler-like security for small businesses.
- How do I know if my data is safe with a VPN? Look for independent audits, transparent privacy policies, and strong encryption standards.
- Do I need a VPN if I already have a firewall? They serve different purposes; a VPN encrypts your traffic, while a firewall blocks unwanted connections.
- Can Zscaler protect personal devices? Zscaler is primarily enterprise-focused; for personal use, consumer security suites or VPNs are more practical.
- How do I switch from a proxy to a VPN? Disable proxy settings and enable the VPN app, then connect to a server.
- Can VPNs help with geo-blocked streaming? Sometimes, but streaming services actively detect and block VPNs; you may need to try different servers.
- What’s zero trust networking? A security model that assumes no device or user is trustworthy by default; continuous verification is required.
Frequently Asked Questions Le vpn piu veloci del 2026 le abbiamo davvero provate
Is a VPN legal in most countries?
VPN legality varies by country. Most places allow personal VPN use, but some jurisdictions restrict or ban VPNs for certain activities.
Do proxies provide encryption?
Most proxies don’t provide encryption. Some secure proxy types like HTTPS proxies offer partial encryption, but they’re not equivalent to VPN encryption.
Can Zscaler be used by individuals?
Zscaler is primarily designed for enterprises. Individuals typically use consumer-grade VPNs or personal security suites.
What’s the difference between SWG and ZTNA?
Secure Web Gateway SWG screens and protects web traffic. Zero Trust Network Access ZTNA focuses on granting access only to authenticated and authorized users and devices.
How do I choose a VPN provider?
Look for a solid privacy policy, independent audits, strong encryption, a good server count and locations, fast speeds, and reliable customer support. Surfshark vpn very slow heres how to fix it fast: quick, practical fixes and setup tips for blazing-fast performance
Can I use a VPN on my mobile device?
Yes, most reputable VPNs offer Android and iOS apps with similar features to desktop versions.
What is DNS leak protection?
DNS leak protection prevents your DNS requests from revealing your real IP address outside the VPN tunnel.
Do VPNs work in schools or workplaces?
In many cases, schools and workplaces block VPN traffic. Check policies and consider legitimate usage, like remote access or privacy protection.
How can I test if my VPN is leaking data?
Use a combination of IP, DNS, and WebRTC leak tests to verify that all traffic is properly routed through the VPN.
Should I use a VPN and a firewall together?
Yes. A VPN protects data in transit, while a firewall blocks unauthorized access. They complement each other for stronger security. Whats a VPN on TikTok and Do You Actually Need One? A Complete Guide for 2026
Sources:
Microsoft edge review vs chrome
Nordvpnのデメリットとは?知っておくべき欠点と評判
10大vpn:2025年最佳VPN全面评测与使用指南
免费梯子 安卓 2026:安全好用的免费vpn推荐与选择指南,安卓免费梯子对比、隐私保护、速度评估、付费升级与合规要点
Unlocking nordvpn for free the real deals and what to watch out for Finding secure vpns on github your guide to open source privacy